Understanding the Purpose of Your Portfolio
Before you start gathering your artwork, ask yourself: what’s the purpose of this portfolio? Are you applying to a specific school or program? Looking for freelance gigs? Or just wanting to build an online presence? Knowing your audience will help you tailor your portfolio to meet their expectations.
Selecting Your Best Work
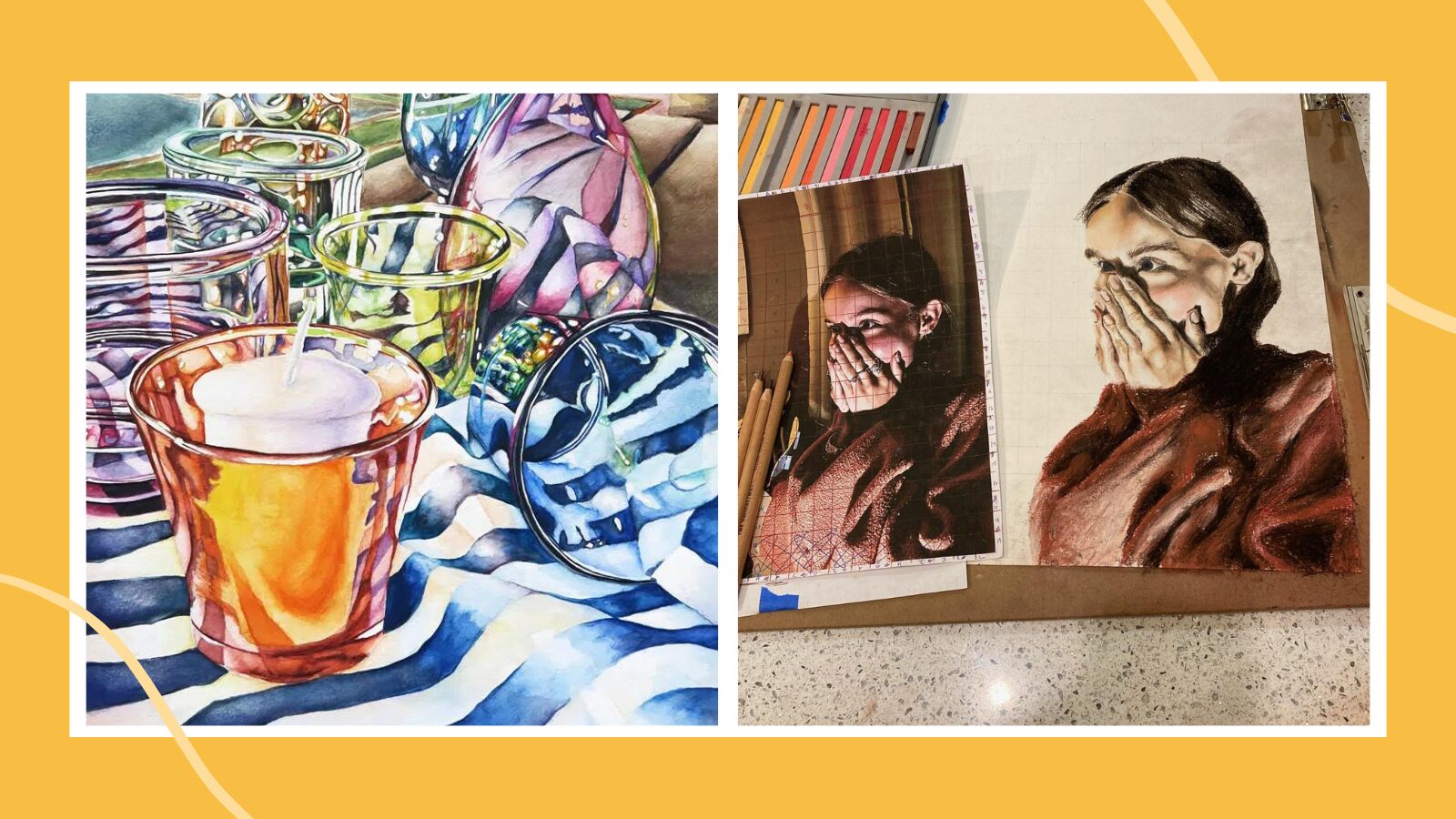
Quality over quantity is key here. Select pieces that not only showcase your technical skills but also reflect your personal style and creativity. Aim for a range of work that demonstrates your versatility. A good rule of thumb is to include 10-20 of your strongest pieces.
Organizing Your Portfolio
Think of your portfolio as a visual story. Start with a strong piece to grab attention, and then arrange the rest in a way that takes the viewer on a journey through your work. Group similar pieces together, and consider the flow from one piece to the next.
Presentation Matters
How you present your work is just as important as the work itself. Ensure that each piece is well-photographed or scanned, and edited to look its best. If you’re creating a physical portfolio, invest in a high-quality portfolio book. For digital portfolios, ensure your website is easy to navigate and visually appealing.
Adding Context
Context can make a huge difference. For each piece, include a brief description or an artist statement. Explain your inspiration, the techniques you used, and any challenges you overcame. This not only gives insight into your creative process but also engages the viewer.
Examples and Inspiration
Looking at examples of successful portfolios can provide inspiration and guidance. Websites like Behance, ArtStation, and personal artist websites are great places to see how other artists present their work. Notice how they use layout, descriptions, and their overall aesthetic to create a cohesive portfolio.
Tips for Success
- Be Authentic: Your portfolio should reflect who you are as an artist. Don’t try to mimic others; showcase your unique voice.
- Keep it Updated: Regularly update your portfolio with new work and remove older pieces that no longer represent your current skill level or style.
- Seek Feedback: Don’t be afraid to ask for feedback from mentors, peers, or industry professionals. Constructive criticism can help you improve.
- Stay Organized: Keep your digital files organized and back them up. Label your pieces clearly and maintain a master list of what’s included in your portfolio.
- Be Professional: Pay attention to details, from your contact information to how you present yourself in an artist bio or resume.
Conclusion
Creating an art portfolio is a dynamic and ongoing process. It’s a reflection of your artistic journey and should evolve as you grow. By thoughtfully curating your work, presenting it professionally, and continuously updating it, you’ll be well on your way to making a lasting impression.
FAQs
1. How often should I update my art portfolio?
Update your portfolio regularly, ideally every few months or whenever you complete a significant new project.
2. Should I include works in progress in my portfolio?
It’s best to include only finished pieces. However, you can share your process through sketches or studies to show your workflow.
3. How do I choose between a physical and digital portfolio?
Consider your audience and purpose. Digital portfolios are versatile and easily accessible, while physical portfolios can make a strong impact in face-to-face situations.
4. Can I include collaborative work in my portfolio?
Yes, but make sure to clearly credit all collaborators and explain your specific contribution to the project.
5. How do I handle portfolio rejections?
Rejections are part of the process. Use them as learning experiences, seek feedback if possible, and continue refining your work and portfolio.